Save Application Explorer filter selections
Valid from Pega Version 7.1.5
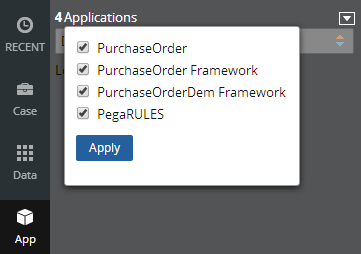
Application scoping control selections made in the Application Explorer are now persisted between sessions. These preferences are stored in an operator record on an access group level. If you delete (and later re-add) an access group on your operator form, the application scoping control defaults to all layers selected:
Configure a Barcode/QR code scanner in a mobile application
Valid from Pega Version 7.1.7
You can configure the Scan Barcode/QR Code action in a mobile application to launch the native Barcode/QR code scanner on a mobile device. In addition to barcode scanning functionality for e-commerce purposes, QR codes can also be used to quickly access a designated URL to download an application or access a website.
Using this action requires that the mobile app either is accessed using the Pega 7 mobile app or is built as a hybrid mobile application in Designer Studio. For more information, see PDN article: How to use the Scan Barcode/QR Code mobile control.
Link configuration in grid columns
Valid from Pega Version 7.1.5
Grid columns now support configuring a link with either simple text (or field value) or with a property reference.
To configure a link, in Designer Studio, add a link control to a section from the Basic control group. Click the gear icon in the link control to open the Cell Properties dialog. In the Link caption field, select either Field Value, Parameter, Text, or Property Reference.
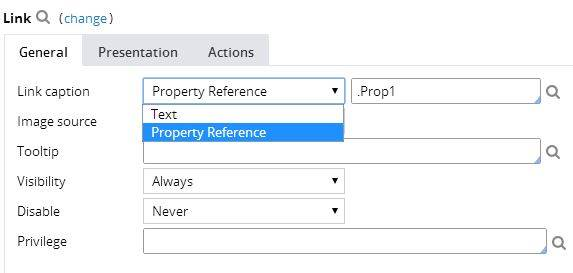
For each selection:
- Field value displays a field value picker
- Parameter displays the list of parameters associated with the section in a dropdown
- Text displays a text input
- Property Reference displays a property picker
Selecting Property Reference allows grid columns to be sorted and filtered, as shown below:
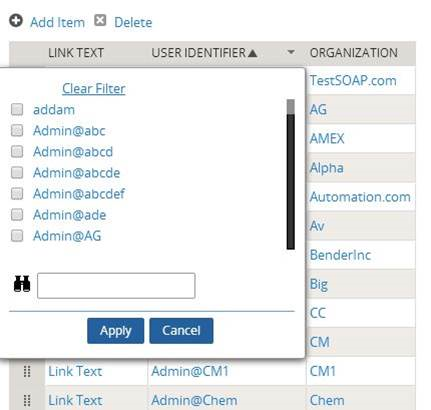
Plan projects using release data
Valid from Pega Version 7.1.7
Requirements and specifications can now be mapped to a target release and iteration within a specific release. Populating these fields allows you to set and publish a release schedule through worksheets generated by the Sizing wizard. Access these fields from the Application Profile landing page or by opening any requirement or specification.
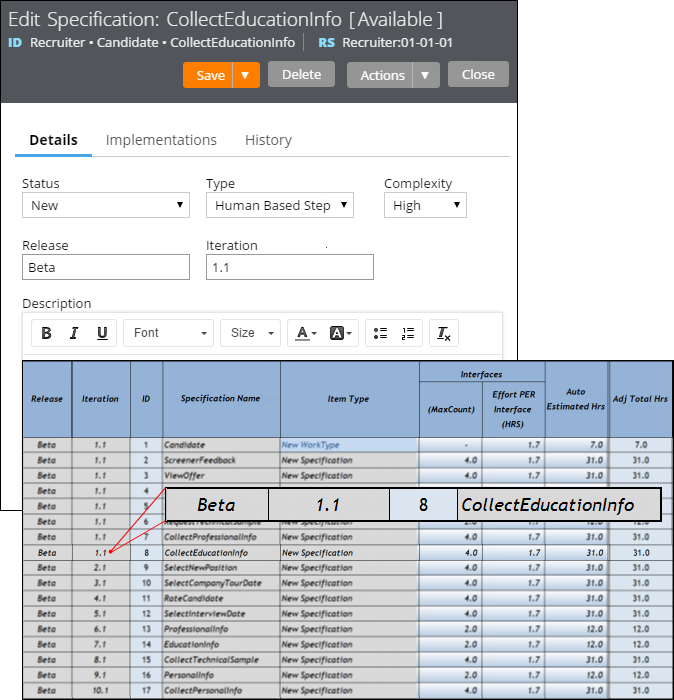
The Release and Iteration fields as they appear in a specification and a corresponding worksheet
The Sizing wizard incorporates values from the Release and Iteration fields for specifications only.
PegaWAI ruleset deprecated in 8.5
Valid from Pega Version 8.5
Accessibility functions that were contained in the PegaWAI ruleset are now integrated into the main Pega Platform™. Consequently, the user interface in your applications now features accessibility functions out of the box, so you no longer need to use the PegaWAI ruleset to ensure accessible behavior in your application.
For more information, see Building an accessible UI.
Support for application-specific REST API calls
Valid from Pega Version 8.5
You can now call an authenticated REST API in the context of any application that is listed on an operator record by using the application alias URL. With the application alias URL, you can also develop REST services without changing the access group in the service package. REST services run in the context of the access group that points to the provided application, instead of the access group that is specified in the service package.
For more information, see Invoking a REST service rule.
Tamper-proof Pega Web Mashup loading
Valid from Pega Version 8.5
To protect your application from hackers, Pega Web Mashup is now loaded in a more secure way. The system generates a channel ID in the mashup code for validation on the server, before passing the mashup request.
For more information, see Creating a mashup.
Upgrade impact
After an upgrade to Pega Platform 8.5, existing mashups, which do not have the channel ID parameter in their code, cannot load and users see the access control warning.
What steps are required to update the application to be compatible with this change?
If you need to maintain full availability of the mashup during the upgrade of the production environment, perform the steps in Migrating existing mashups.
Automatic separation of date input
Valid from Pega Version 8.5
Date fields in Date Time controls now automatically divide strings of input into days, months, and years. In single fields, the system adds slashes (/) as the user types the value. For example, an input string of 10102020 becomes 10/10/2020. In separate day/month/year fields, the system automatically switches from one field to the next as the user types the value. This enhancement improves the user experience by helping to users provide input in a more convenient and time-efficient manner.
For more information, see Configuring a Date Time control.
Improvements to OAuth 2.0 Services with Token Introspection Service and Token Denylist Service
Valid from Pega Version 8.5
Increase the security of user sessions by using the newly supported Token Introspection and Denylist services for OAuth 2.0.
Token Introspection service
Use the Token Introspection service to validate JSON Web Tokens (JWT). The Token Introspection service requires authentication.
Pega now uses OAuth 2.0 access tokens called Authorized Access Tokens (AAT).
Token Introspection service endpoint
The Token Introspection service endpoint provides the information about the status of access token and refresh token. Token introspection can be used to validate if a given token is still active or inactive. The token introspection endpoint determines whether the token is valid. The status indicates whether an access token or refresh token is valid or invalid:
- Valid tokens have the
“active”:truestatus - Invalid tokens have the
“active” :falsestatus.
The inactive status can also be due to revocation.
Token Denylist service
You can add tokens to the deny list in cases where suspicious activity might have occurred. The Token Denylist service provides a method for denying user access to the application by revoking the user's access token. This service can prevent a token from being used more than the specified number of times, which can be helpful in preventing replay attacks. Stolen tokens should be revoked using this service. A GET API is also available to get the list of denied tokens.
Keys endpoint
Pega Platform™ is changing from using opaque tokens to JSON Web (JWT) tokens. If this JWT is used by any other system, the public key is needed for signature verification. A new endpoint is exposed to provide these public keys in JWK format: https://host:port/prweb/api/oauth2/v1/token/keys.
For more information, see OAuth 2.0 Management Services.
Search and Reporting does not index large items
Valid from Pega Version 8.5
When using the Search and Reporting (SRS) microservice in Pega Platform™ 8.5, you might encounter problems with indexing large out-of-the-box rules. The issue is not visible in Queue Processors, but you can access logs to verify which items the system does not index.

